Kali NetHunter
Table of Contents
- Overview
- 1.0 NetHunter Editions
- 2.0 NetHunter Supported Devices and ROMs
- 3.0 Downloading NetHunter
- 4.0 Building NetHunter
- 5.0 Installing NetHunter on top of Android
- 6.0 Post Installation Setup
- 7.0 Kali NetHunter Application
- 8.0 Porting NetHunter to New Devices
- 9.0 Known Working Hardware
- 10.0 NetHunter Apps
- 11.0 Useful Links
Kali NetHunter is a free & Open-source Mobile Penetration Testing Platform for Android devices, based on Kali Linux.
Overview
Kali NetHunter is available for un-rooted devices (NetHunter Rootless), for rooted devices that have a custom recovery (NetHunter Lite), and for rooted devices with custom recovery for which a NetHunter specific kernel is available (NetHunter).
The core of Kali NetHunter, which is included in all three editions, comprises of:
Kali Linux container that includes all the tools and applications that Kali Linux provides
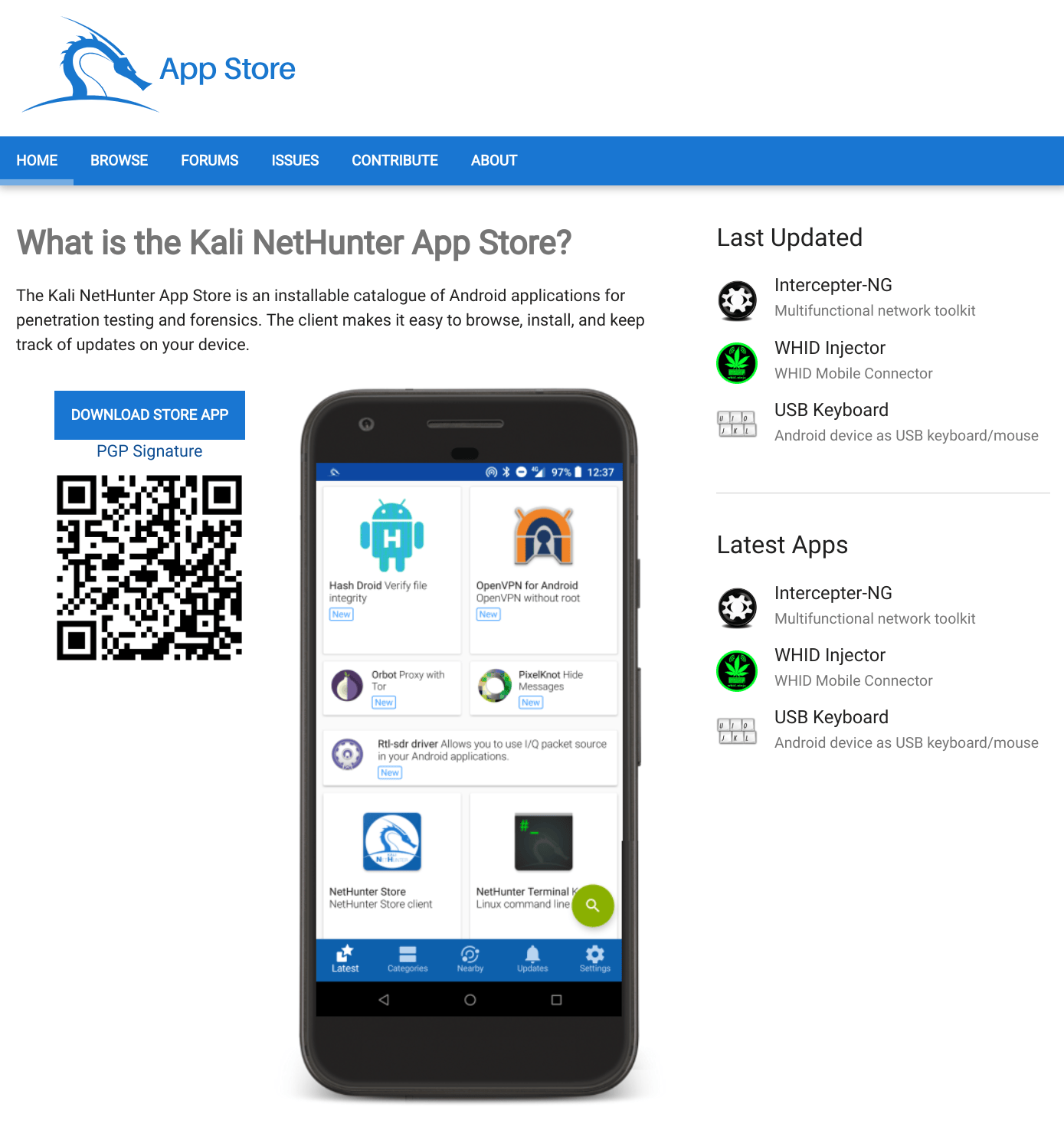
Kali NetHunter App Store with dozens of purpose-built security apps
Android client to access the Kali NetHunter App Store
Kali NetHunter Desktop Experience (KeX) to run full Kali Linux desktop sessions with support for screen mirroring via HDMI or wireless screen casting
The Kali NetHunter App Store can be accessed through the dedicated client app or via the web interface.
Figure 3: Kali NetHunter App StoreBoth rooted editions provide additional tools & services. A custom kernel can extend that functionality by adding additional network and USB gadget drivers as well as Wi-Fi injection support for selected Wi-Fi chips.
Figure 3: The Kali NetHunter App is available in both rooted editions (NetHunter Lite & NetHunter).Beyond the penetration testing tools included in Kali Linux, NetHunter also supports several additional classes, such as HID Keyboard Attacks, BadUSB attacks, Evil AP MANA attacks, and many more.
For more information about the moving parts that make up NetHunter, check out our NetHunter Components page. Kali NetHunter is an Open-source project developed by Kali and the community.
1.0 NetHunter Editions
NetHunter can be installed on almost every Android device under the sun using one of the following editions:
| Edition | Usage |
|---|---|
| NetHunter Rootless | The core of NetHunter for unrooted, unmodified devices |
| NetHunter Lite | The full NetHunter package for rooted phones without a custom kernel. |
| NetHunter | The full NetHunter package with custom kernel for supported devices |
The following table illustrates the differences in functionality:
| Feature | NetHunter Rootless | NetHunter Lite | NetHunter |
|---|---|---|---|
| App Store | Yes | Yes | Yes |
| Kali cli | Yes | Yes | Yes |
| All Kali packages | Yes | Yes | Yes |
| KeX | Yes | Yes | Yes |
| Metasploit w/o DB | Yes | Yes | Yes |
| Metasploit with DB | No | Yes | Yes |
| NetHunter App | No | Yes | Yes |
| Requires TWRP | No | Yes | Yes |
| Requires Root | No | Yes | Yes |
| Wi-Fi Injection | No | No | Yes |
| HID attacks | No | No | Yes |
| BT Arsenal | No | No | Yes |
| CARsenal | No | No | Yes |
The installation of NetHunter Rootless is documented here: NetHunter-Rootless
The NetHunter-App specific chapters are only applicable to the NetHunter & NetHunter Lite editions.
The Kernel specific chapters are only applicable to the NetHunter edition.
2.0 NetHunter Supported Devices and ROMs
NetHunter Lite can be installed on all Android devices that are rooted and have a custom recovery. The full NetHunter experience requires a devices specific kernel that has been purpose built for Kali NetHunter. The NetHunter GitLab repository contains over 230 kernels for over 100 devices. Kali Linux publishes images for the most popular devices on the NetHunter download page. The following live reports are generated automatically by GitLab CI:
- List of quarterly published official NetHunter images
- List of all NetHunter supported kernels
- List of devices which NetHunter can be put on
3.0 Downloading NetHunter
Official release NetHunter images for your specific supported device can be download from the Kali Linux page located at the following URL:
Once the zip file has downloaded, verify the SHA256 sum of the NetHunter zip image against the values on the download page. If the SHA256 sums do not match, do not attempt to continue with the installation procedure.
4.0 Building NetHunter
Those of you who want to build a NetHunter image from our GitLab repository may do so using our Python build scripts. Check out our Building NetHunter page for more information. You can find additional instructions on using the NetHunter installer builder or adding your own device in the README located in the nethunter-installer git repository.
5.0 Installing NetHunter on top of Android
Now that you’ve either downloaded a NetHunter image or built one yourself, the next steps are to prepare your Android device and then install the image. “Preparing your Android device” includes:
unlocking your device and updating it to stock AOSP or LineageOS (CM). (Check point 2.0 for supported roms).
installing Team Win Recovery Project as a custom recovery.
installing Magisk to root the device.
Disabling force encryption may be required if TWRP cannot access the data partition.
Once you have a custom recovery, all that remains is to flash the NetHunter installer zip file onto your Android device.
Flash in Magisk if disabled force encrpytion is not available
6.0 Post Installation Setup
- Open the NetHunter App and start the Kali Chroot Manager.
- Install the Hacker Keyboard from the NetHunter Store using the NetHunter Store app.
- Install any other apps from the NetHunter Store as required.
- Configure Kali Services, such as SSH.
- Set up custom commands.
- Initialize the Exploit-Database.
7.0 Kali NetHunter Application
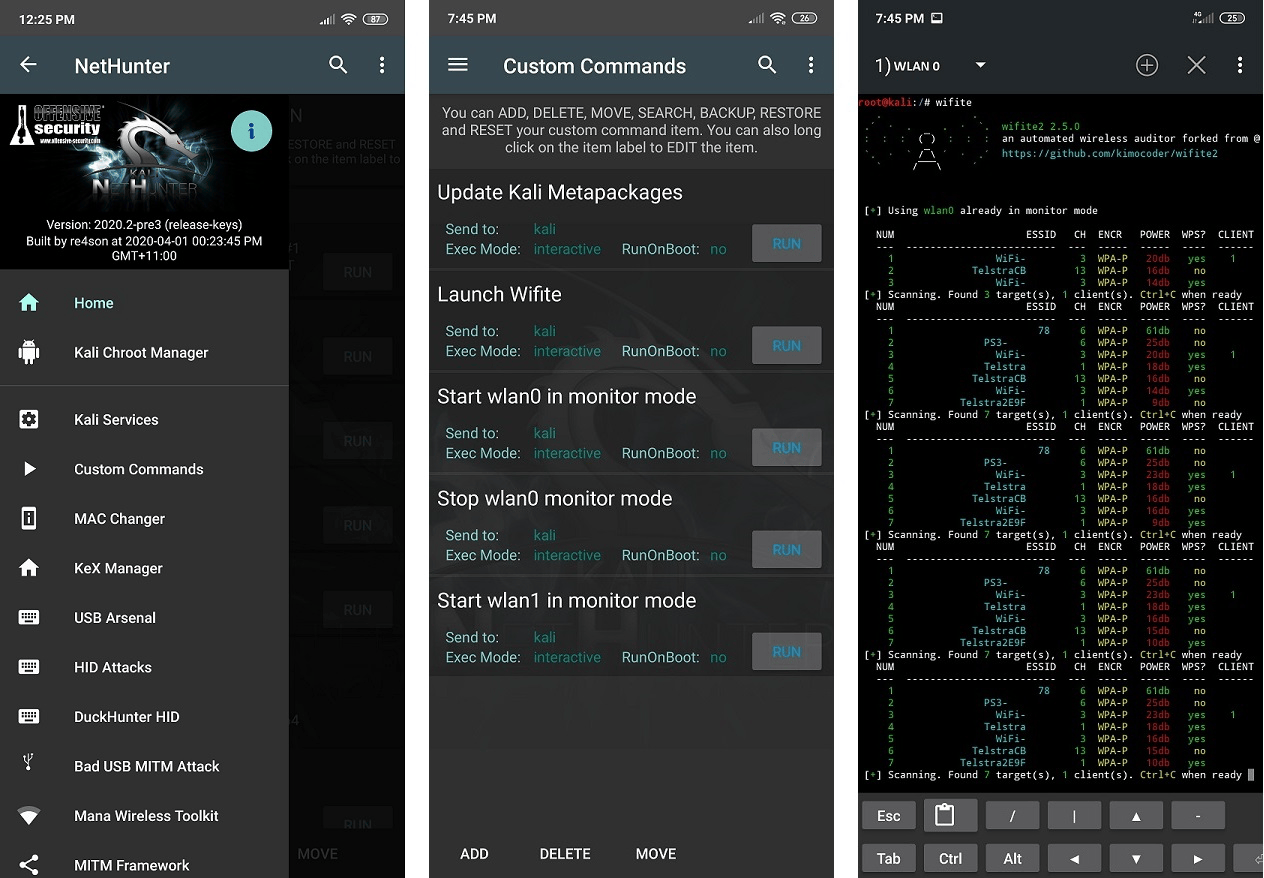
This is an Android APK that contains most of the Kali Nethunter userspace tools. It includes status information and tools to manage Nethunter itself (the kernel and the chroot), tools to as well as a bunch of tools and attacks.
Attacks will be greyed out if the chroot is not running. Some of the attacks will prompt you to download additional requirements on first use.
Nethunter management
- Home Screen - General information panel, network interfaces and HID device status.
- Kali Chroot Manager - For managing chroot metapackage installations.
- Settings - Select bootanimation, and modify various settings.
- Kernel - Search, download, and flash kernel
- Modules - Load modules
Tools
- Kali Services - Start / stop various chrooted services. Enable or disable them at boot time.
- Custom Commands - Add your own custom commands and functions to the launcher.
Attacks
- KeX Manager - Set up an instant VNC session with your Kali chroot.
- MAC Changer - Change your Wi-Fi MAC address (only on certain devices)
- Audio Manager - Enable audio for KeX.
- USB Arsenal - Control the USB gadget configurations.
- HID Attacks - Various HID attacks, Teensy style.
- DuckHunter HID - Rubber Ducky style HID attacks.
- BadUSB MITM Attack - Nuff said.
- Wifipumpkin - Setup a malicious Access Point with captive portal at the click of a button.
- WPS Attacks - WPS attacks using OneShot.
- Bluetooth Arsenal - Recon, spoof, listen to or inject audio to various Bluetooth devices.
- Social Engineer Toolkit - Build your own phishing email template for Social Engineer Toolkit.
- MITM Framework - Inject binary backdoors into downloaded executables on the fly.
- NMap Scan - Quick Nmap scanner interface.
- Metasploit Payload Generator - Generating Metasploit payloads on the fly.
- Searchsploit - Easy searching for exploits in Exploit-Database.
- Pineapple Connector - Provide Wi-Fi via Android for a Hak5 WiFi Pineapple over USB
- Wardriving - Passively sniff nearby Wi-Fi networks
- CARsenal - Automotive Security tools.
8.0 Porting NetHunter to New Devices
If you’re interested in porting NetHunter to other Android devices, check out the following links. If your port works, make sure to tell us about it so we can include these kernels in our releases!
- Getting Started manually
- Getting Started with kernel builder
- Patching a Kernel
- Configuring a Kernel
- Adding Your Device
9.0 Known Working Hardware
- Wireless Cards
- SDR - RTL-SDR (based on RTL2832U)
- Bluetooth adapters - Sena UD100, TP-Link UB500, generic CSR4.0 adapter
10.0 NetHunter Apps
11.0 Useful Links
Updated on: 2025-Sep-13
Authors:
Re4son
,
yesimxev