Tool Documentation:
Screenshots
Packages and Binaries:
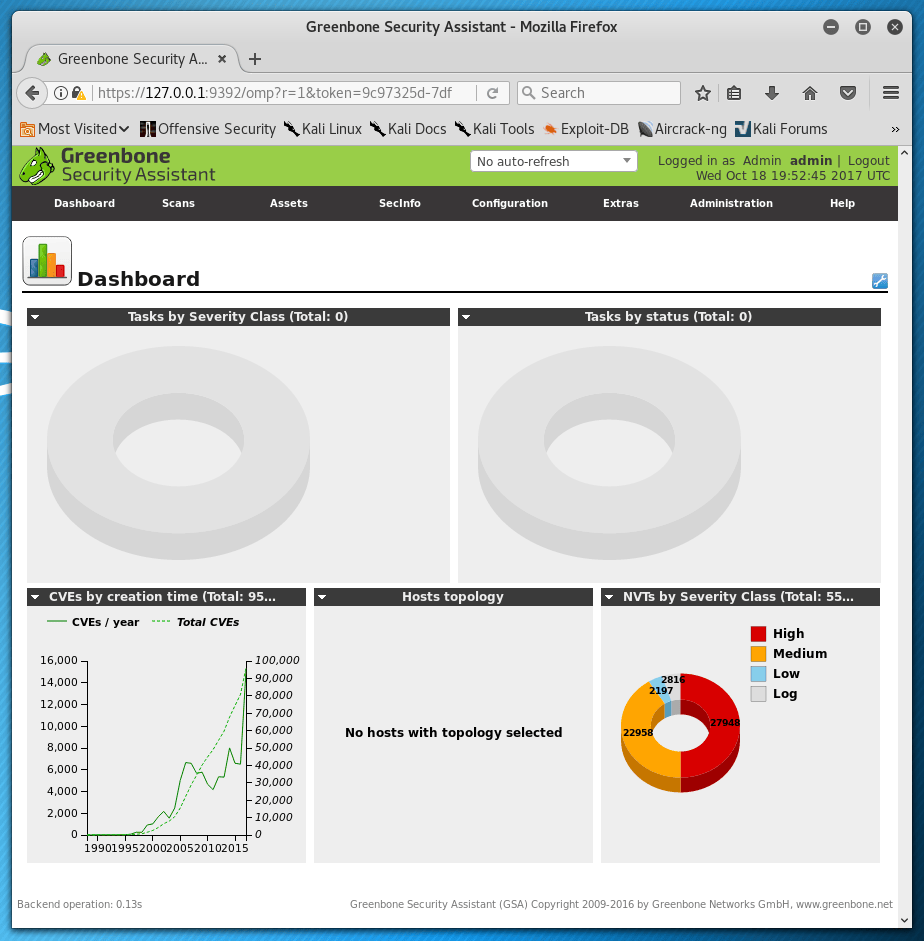
gvm
Remote network security auditor - metapackage and useful scripts
The Greenbone Vulnerability Manager is a modular security auditing tool,
used for testing remote systems for vulnerabilities that should be fixed.
This package installs all the required packages. It provides scripts to setup, start and stop the GVM services.
The tool was previously named OpenVAS.
Installed size: 48 KB
How to install: sudo apt install gvm
Dependencies:
- gsad
- gvmd
- notus-scanner
- openvas-scanner
- ospd-openvas
- psmisc
- rsync
- xsltproc
gvm-check-setup
root@kali:~# gvm-check-setup -h
gvm-check-setup 25.04.0
This script is provided and maintained by Debian and Kali.
Test completeness and readiness of GVM-25.04.0
Step 1: Checking OpenVAS (Scanner)...
OK: OpenVAS Scanner is present in version 23.38.1.
OK: Notus Scanner is present in version 22.7.2.
ERROR: No CA certificate file for Server found.
FIX: Run 'sudo runuser -u _gvm -- gvm-manage-certs -a -f'.
ERROR: Your GVM-25.04.0 installation is not yet complete!
Please follow the instructions marked with FIX above and run this
script again.
IMPORTANT NOTE: this script is provided and maintained by Debian and Kali.
If you find any issue in this script, please report it directly to Debian or Kali
gvm-setup
root@kali:~# gvm-setup -h
This script is provided and maintained by Debian and Kali.
If you find any issue in this script, please report it directly to Debian or Kali
[>] Starting PostgreSQL service
[>] Creating GVM's certificate files
[>] Creating PostgreSQL database
[i] User _gvm already exists in PostgreSQL
[i] Database gvmd already exists in PostgreSQL
[i] Role DBA already exists in PostgreSQL
[*] Applying permissions
GRANT ROLE
[i] Extension uuid-ossp already exists for gvmd database
[i] Extension pgcrypto already exists for gvmd database
[i] Extension pg-gvm already exists for gvmd database
[>] Migrating database
[>] Checking for GVM admin user
[*] Configure Feed Import Owner
[*] Update GVM feeds
Running as root. Switching to user '_gvm' and group '_gvm'.
Trying to acquire lock on /var/lib/openvas/feed-update.lock
Acquired lock on /var/lib/openvas/feed-update.lock
gvm-start
root@kali:~# gvm-start -h
[>] Please wait for the GVM services to start.
[>]
[>] You might need to refresh your browser once it opens.
[>]
[>] Web UI (Greenbone Security Assistant): https://127.0.0.1:9392
gvm-stop
root@kali:~# gvm-stop -h
[>] Stopping GVM services
* gsad.service - Greenbone Security Assistant daemon (gsad)
Loaded: loaded (/usr/lib/systemd/system/gsad.service; disabled; preset: disabled)
Active: inactive (dead)
Docs: man:gsad(8)
https://www.greenbone.net
* gvmd.service - Greenbone Vulnerability Manager daemon (gvmd)
Loaded: loaded (/usr/lib/systemd/system/gvmd.service; disabled; preset: disabled)
Active: inactive (dead)
Docs: man:gvmd(8)
Mar 12 06:44:02 kali systemd[1]: Starting gvmd.service - Greenbone Vulnerability Manager daemon (gvmd)...
Mar 12 06:44:02 kali systemd[1]: gvmd.service: Can't open PID file '/run/gvmd/gvmd.pid' (yet?) after start: No such file or directory
Mar 12 06:44:14 kali systemd[1]: gvmd.service: Deactivated successfully.
Mar 12 06:44:14 kali systemd[1]: Stopped gvmd.service - Greenbone Vulnerability Manager daemon (gvmd).
* ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)
Loaded: loaded (/usr/lib/systemd/system/ospd-openvas.service; disabled; preset: disabled)
Active: inactive (dead)
Docs: man:ospd-openvas(8)
man:openvas(8)
Mar 12 06:44:00 kali systemd[1]: Starting ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)...
Mar 12 06:44:02 kali systemd[1]: Started ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas).
Mar 12 06:44:14 kali systemd[1]: Stopping ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas)...
Mar 12 06:44:15 kali systemd[1]: ospd-openvas.service: Deactivated successfully.
Mar 12 06:44:15 kali systemd[1]: Stopped ospd-openvas.service - OSPd Wrapper for the OpenVAS Scanner (ospd-openvas).
Mar 12 06:44:15 kali systemd[1]: ospd-openvas.service: Consumed 2.163s CPU time over 15.554s wall clock time, 102.2M memory peak.
* notus-scanner.service - Notus Scanner
Loaded: loaded (/usr/lib/systemd/system/notus-scanner.service; disabled; preset: disabled)
Active: inactive (dead)
Docs: https://github.com/greenbone/notus-scanner
Mar 12 06:44:00 kali systemd[1]: Starting notus-scanner.service - Notus Scanner...
Mar 12 06:44:00 kali systemd[1]: Started notus-scanner.service - Notus Scanner.
Mar 12 06:44:01 kali notus-scanner[243784]: 2026-03-12 06:44:01,428 notus-scanner: INFO: (notus.scanner.daemon) Starting notus-scanner version 22.7.2.
Mar 12 06:44:14 kali systemd[1]: Stopping notus-scanner.service - Notus Scanner...
Mar 12 06:44:14 kali systemd[1]: notus-scanner.service: Deactivated successfully.
Mar 12 06:44:14 kali systemd[1]: Stopped notus-scanner.service - Notus Scanner.
Learn more with OffSec
Want to learn more about gvm? get access to in-depth training and hands-on labs:
Updated on: 2026-Mar-13